逆向攻防世界CTF系列11-maze
逆向攻防世界CTF系列11-maze迷宫问题:迷宫问题 - CTF Wiki (ctf-wiki.org) 64位无壳 12345678910111213141516171819202122232425262728293031323334353637383940414243444546474849505152535455565758596061626364656667__int64 __fastcall main(__int64 a1, char **a2, char **a3){ const char *v3; // rsi signed __int64 v4; // rbx signed int v5; // eax char v6; // bp char v7; // al const char *v8; // rdi __int64 v10; // [rsp+0h] [rbp-28h] v10 = 0LL; puts("Input flag:"); scanf("%s", &s1, 0LL);...
MyBatis
MyBatis[TOC] 一、MyBatis简介MyBatis下载:https://github.com/mybatis/mybatis-3 1.1 MyBatis历史MyBatis最初是Apache的一个开源项目iBatis, 2010年6月这个项目由Apache Software Foundation迁移到了Google Code。随着开发团队转投Google Code旗下, iBatis3.x正式更名为MyBatis。代码于2013年11月迁移到Github。 iBatis一词来源于“internet”和“abatis”的组合,是一个基于Java的持久层框架。 iBatis提供的持久层框架包括SQL Maps和Data Access Objects(DAO)。 1.2 MyBatis特性 MyBatis 是支持定制化 SQL、存储过程以及高级映射的优秀的持久层框架 MyBatis 避免了几乎所有的 JDBC 代码和手动设置参数以及获取结果集 MyBatis可以使用简单的XML或注解用于配置和原始映射,将接口和Java的POJO(Plain Old Java...
计算机保研复习-数据库
数据库复习一、基本概念数据库:长期存储在计算机内、有组织、可共享的大量数据的集合,数据库中的数据按照一定的数据模型组织、储存,具有较低的冗余度、较高的数据独立性和易扩展性。 数据库分类:关系数据库、非关系型数据库(NoSQL、MongoDB)、图数据库(Neo4j)、内存数据库(Redis) 数据库管理系统:位于用户与操作系统之间的数据管理软件 数据库系统:由数据库、数据库管理系统、应用程序和数据库管理员组成的存储、管理、处理和维护数据的系统 数据库有什么类型的数据库、关系型数据库的特点 特点: 结构化数据存储:使用关系来组织和存储数据,数据以行和列的形式组织,表格之间通过键值进行关联。 SQL语言:使用SQL来进行数据的查询、插入、更新和删除等操作。 事务支持:支持ACID特性,保证数据库操作的可靠性和一致性。 数据完整性:关系型数据库支持各种约束,可以确保数据的完整性和一致性。 复杂查询支持:关系型数据库支持复杂的查询操作,包括联合查询、嵌套查询、聚合函数、子查询等 二、数据库体系结构2.1...
servlet
一.servlet简介Servlet含义是服务器端的小程序 二.web.xml配置 12345678910111213141516171819202122<?xml version="1.0" encoding="UTF-8"?><web-app xmlns="http://xmlns.jcp.org/xml/ns/javaee" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://xmlns.jcp.org/xml/ns/javaee http://xmlns.jcp.org/xml/ns/javaee/web-app_4_0.xsd" version="4.0"> <servlet> ...
逆向攻防世界CTF系列10-csaw2013reversing2
逆向攻防世界CTF系列10-csaw2013reversing232位无壳 提示:听说运行就能拿到Flag,不过菜鸡运行的结果不知道为什么是乱码 运行果然出乱码… 解法1:静态分析 大概是要MessageBoxA输出结果flag,但是我们输出的是乱码,可能是if语句没有执行,此外,if 语句中还有个exit函数 我们没输出flag的原因是因为sub_401000没有执行,我们想办法让他执行 左侧的MessageBoxA:一个没有被调用的弹框函数 修改点1:红框1处jzn改为jmp就是无条件跳转, 修改点2:jmp short loc_4010EF改为 jmp short loc_4010B9,避免让他执行exit函数。 修改点3:int 3(__debugbreak();) 改为 nop __debugbreak () 是一个内置函数,用于在程序运行时生成一个软件断点,从而暂停程序执行并等待调试器连接。 一旦你的进程执行到int 3指令时,操作系统就将它暂停。在Linux上,这会给该进程发送一个SIGTRAP信号。 NOP(No...
计算机保研复习-数据结构
数据结构一、线性表1.1 数组和链表的区别线性表是具有相同数据类型的n个数据元素的有限序列 物理存储结构不同: 数组是顺序存储结构,存储长度是固定的,它不能适应数据动态增减的情况; 链表是链式存储结构,能够动态分配存储空间以适应数据动态增减的情况; 内存分配方式不同: 数组的存储空间一般采用静态分配; 链表的存储空间一般采用动态分配; 元素的存取方式不同: 数组元素为直接存取; 链表元素的存取需要遍历链表; 元素的插入和删除方式不同: 数组进行元素插入和删除时,需要移动数组的元素; 链表进行元素插入和删除时,无需移动链表内的元素; 1.2 链表种类 单链表 双链表 循环单链...
计算机保研复习-操作系统
操作系统一、操作系统概述==1.1...
计算机保研复习-计算机网络
计算机网络定义:计算机网络就是一些互联的、自治的计算机系统的集合。 一、大致1.1 网络层协议 IP:IP是互联网协议,它负责将数据包从源主机传输到目标主机,通过IP地址来标识主机和网络。 ICMP: 它用于报告错误、测试主机的可达性以及其他网络状态信息。 IP 层的协议,封装在IP数据报中。 常见应用: Ping命令用来测试两台主机之间的连通性 Traceroute用来跟踪分组经过的路由 IGMP:IGMP是用于在IP网络上管理多播组的协议。它允许主机加入或离开多播组,以便有效地传输多播数据。 ARP:实现IP地址到MAC地址的映射 OSPF:开放最短路径优先协议,它采用洪泛法向本自治系统中的所有路由器发送信息在IP网络中确定最短路径。 传输层协议:TCP、UDP 1.2...
计算机保研复习-C++和JAVA
C++和JAVA 首先应该清楚,Java 是由 C++发展而来的,保留了 C++的大部分内容。但 Java 的句法更清晰、规模更小、更易学。 1. 解释对编译Java是一种解释性语言,其在执行时会被“翻译”为二进制形式,也就是jvm去解释它。而C++则是编译语言,意味着程序只能在特定操作系统上编译并在特定系统上运行,也就是说C++一步到位成机器语言的。 2. 指针Java 没有指针的概念。在 C/C++中,指针操作内存时,经常会出现错误。而在Java中是没有指针这一概念的,因此也有效地防止了一系列由指针引起的操作层失误(如指针悬空所造成的系统崩溃),更有利于 Java 程序的安全。 3. 内存安全Java是一种内存安全型语言,意味着大家可以为给定数组分配任意参数,即使超出范围也只会返回错误提示。C++更为灵活,但代价是一旦分配的参数超出资源范围,则会引起错误甚至严重崩溃。 4. 多重继承Java不支持多重继承。多重继承,它允许多父类派生一个子类。也就是说,一个类允许继承多个父类。尽管多重继承功能很强,但使用复杂,而且会引起许多麻烦,编译程序实现它也很不容易。所以...
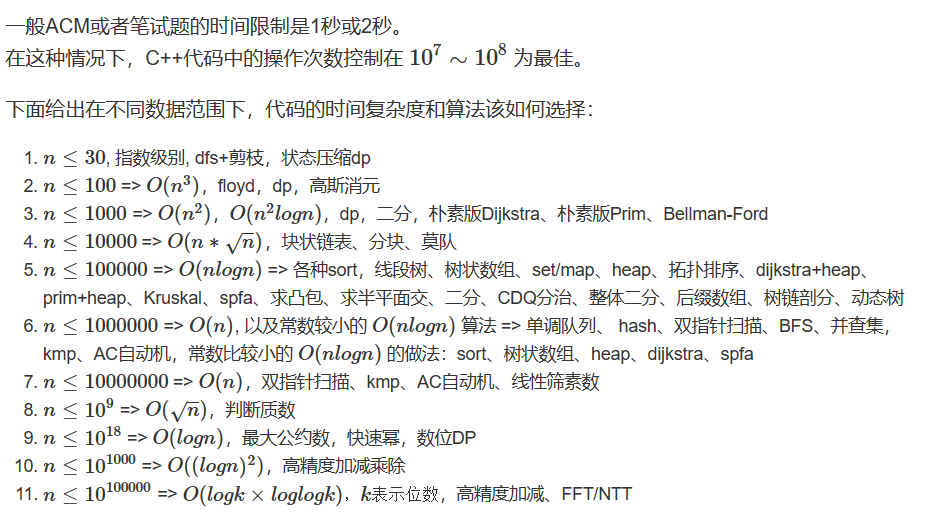
计算机保研复习-算法基础课(java&&C++)
算法基础课(java&&C++) 第一章 基础算法1.1 快速排序123456789101112131415161718192021222324252627#include <iostream>using namespace std;const int N = 1000010;int q[N];void quick_sort(int l, int r){ if (l >= r) return; int i = l - 1, j = r + 1, x = q[l + r >> 1]; while (i < j){ do i ++ ; while (q[i] < x); do j -- ; while (q[j] > x); if (i < j) swap(q[i], q[j]); } quick_sort(l, j); quick_sort(j + 1, r);}int...